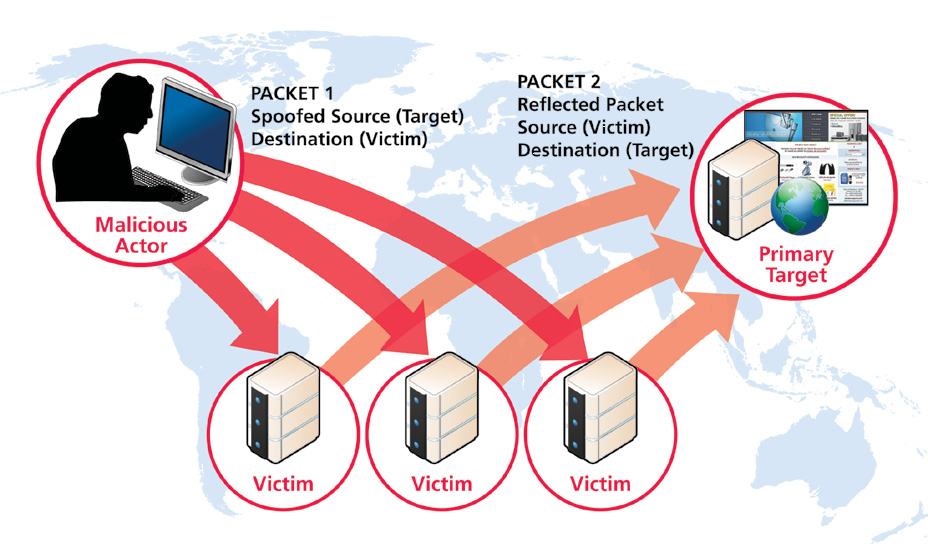
DrDoS Attacks
DrDoS attacks abuse Internet protocols for anonymity and larger attack sizes.
Attacks involving DrDoS techniques accounted for 39 percent of all distributed denial of service (DDoS) attacks in Q4 2014. Starting in 2012, there was a significant increase in the use of a specific distributed denial of service (DDoS) methodology known as DrDoS.
DrDoS attacks have been a persistent and effective type of DDoS attack for more than 10 years. The technique shows no signs of obsolescence; it continues to grow in effectiveness and popularity.