Enterprise Application Access
Application Access Redefined: Simple. Secure. Convenient.
Enterprise Application Access is a unique cloud architecture
Enterprise Application Access is a unique cloud architecture that closes all inbound firewall ports, while ensuring that only authorized users and devices have access to the internal applications they need — not the entire network. No one can access applications directly because they are hidden from the Internet and public exposure.
Enterprise Application Access integrates data path protection, single sign-on, identity access, application security, and management visibility and control into one service.
And device posture capabilities allow security and threat intelligence signals to enhance contextual access to corporate applications.
It can be deployed in minutes through a unified portal with a single point of control, in any network environment, and at a fraction of the cost of traditional solutions. The result is a secure-access delivery model that enables a zero CapEx, low OpEx model for critical workloads deployed in any environment.
Benefits
- Reduce the risk of compromise from employees, third-party contractors, partners, and mobile users — regardless of their location — by delivering secure application access without the need for network access
- Deliver better-informed decision-making through enhanced visibility and a more granular understanding of users based on security signals, including device posture, threat intelligence, and endpoint compromise
- Eliminate the operational cost and risk involved in maintaining and patching VPNs, and other appliance-based solutions, for secure application access
- Enable high performance at low cost in a branch environment by retiring Multi-Protocol Label Switching (MPLS) and using application access over the Internet as transport
- Reduce your technical complexity and debt with a user/application-centric model for secure access, by building on the unmatched scalability of the Akamai Intelligent Edge platform
- Leverage the power of multiple clouds by enabling secure access to applications across AWS, Azure, and Google Cloud, as well as web and SaaS applications — using a single secure portal for access
- Accelerate the pace of mergers and acquisitions by enabling shared access to applications, without complex or costly network consolidation or re-architecture
“If Akamai’s capabilities were to be maintained in-house, we would have to hire, train, and retain substantial and expensive security resources. We find that it’s more cost-effective to use Akamai’s products than attempt to hire and retain scarce security talent.”
— Head of Security and Compliance, Forrester TEI Report
Enterprise Application Access
Secure, Simple, and Fast Application Access
Secure access to the right application, for the right user, at the right time has become difficult and complex because of the widely distributed nature of users and applications. The definition of a user has evolved to be much more than an employee; this can be a supplier, partner, customer, developer, or an employee of a newly acquired company. Applications now have wider definitions that include multiple types (legacy, web, or SaaS) and locations (data center, Internet, and public cloud).
A New Approach Is Needed to Deliver Zero Trust Access
Legacy network security tools, built for the outdated notion of a secure perimeter, have not kept pace with today’s need for secure access. These traditional technologies leave organizations vulnerable to attack by bad actors who move laterally inside the network. The ideal solution to this problem is one that grants user access to specific applications and not to entire networks or network segments, as VPN tunnels do. A cloud-delivered, identity-aware, high-performance service is required to provide secure application access for users whenever and wherever they need it.
Why Akamai for Zero Trust Access
Akamai’s edge platform enables your secure digital transformation. It gives you the scalability, visibility, and simplicity needed to adapt your business: Quickly onboard employees from a merger or acquired company, enable manufacturing or production in different markets or geographies, easily add and remove contractors to adapt to changing business needs, and move applications to the cloud cost-effectively without sacrificing security. Akamai’s platform allows you to deploy IT staff to important business initiatives, rather than maintaining outdated legacy VPN security architecture.
How it works?
Enterprise Application Access
An Enterprise Application Access connector connects to your application server, then dials out to the Enterprise Application Access service on TCP port 443, commonly open for outbound communication on most companies’ firewalls. No additional hardware or software is required.
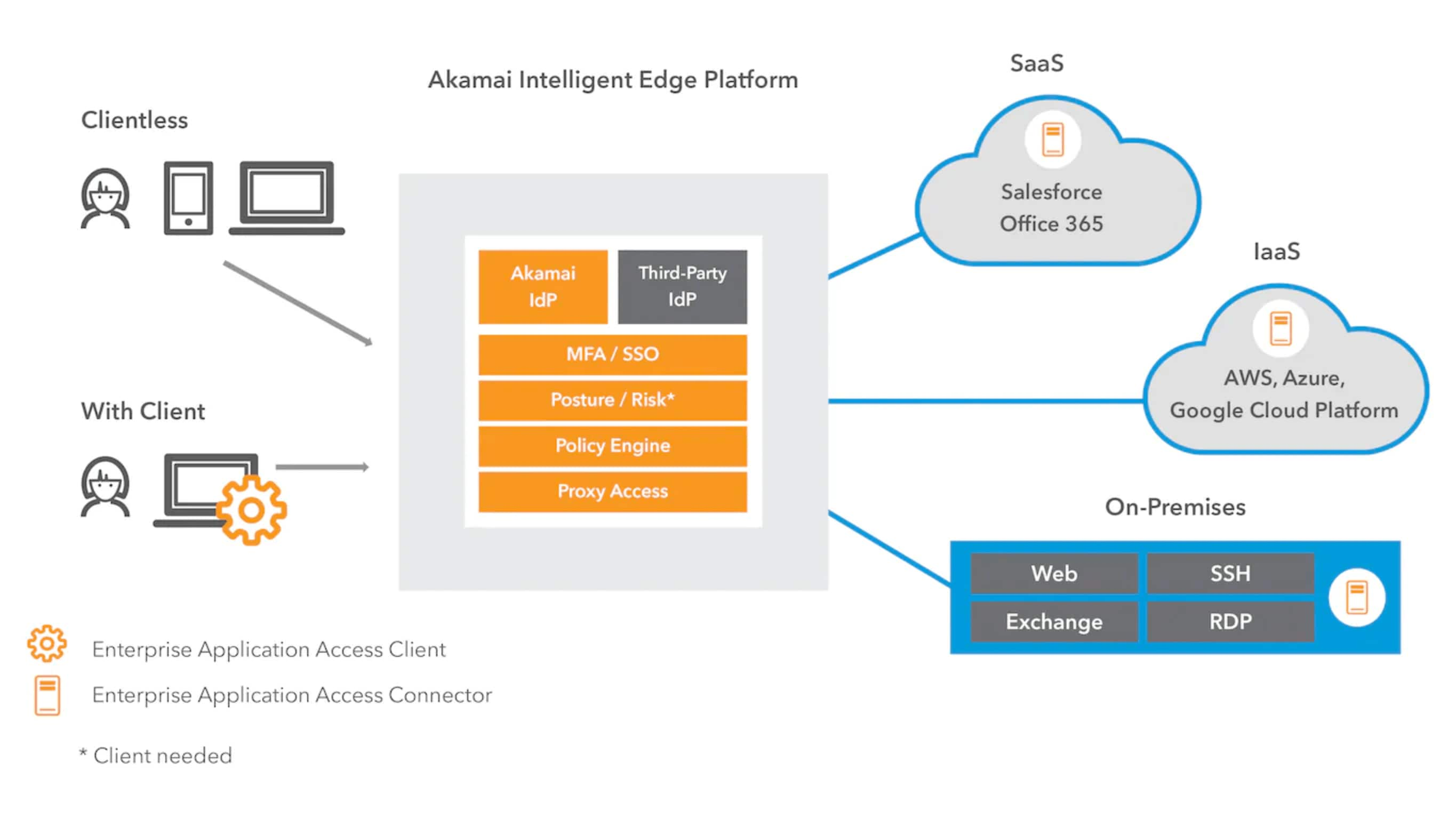
The service is architected based on three primary components:
- Data Edge: Provides the data plane between the user and the application, as well as data security, application performance, and optimization components.
- Management Edge: Provides management, logging, reporting, and configuration capabilities. The management and data edges are based on a secure, multi-tenant architecture. In addition to the multi-tenant data cloud, you have the option to select a dedicated single-tenant data cloud that can be configured to only process a single user’s traffic.
- Enterprise Connectors: Users connect to the Enterprise Application Access single sign-on service through a URL entered into their browsers. They simply provide their credentials to gain access to applications. Enterprise Application Access can also integrate with existing SSO products. Akamai’s solution captures information such as user identity and contextual signals, as well as device posture, meaning device vulnerability and threat intelligence signals, to build out robust risk profiles that assist with secure access decision-making.
Enterprise Application Access works with all applications — legacy on-premises, IaaS, and SaaS.
Key Capabilities
- Secure, clientless, and private application access to nonbrowser TCP/UDP applications using a lightweight client lightweight client
- Secure, clientless, and private application access to web applications and secure RDP/SSH/VDI application access via a clientless browser, without exposing the network or applications to the Internet
- Unlimited connectors for load balancing to deliver vertical and horizontal scaling deployment in data center, cloud, and hybrid environments, as well as to secure connectivity to applications
- Granular, adaptive controls for granting intelligent access, including IP address-based access and role/group, time, and location-based application access control and authorization
- Enable more granular access decision-making through the capture of data for user authenticity including key signals such as OS, browser and client versions, firewall, antivirus/malware status, and
device/user certificate validation - Built-in identity functionality as well as the flexibility to work with a variety of identity and SSO providers
- Flexibility to create web application path-based policies for user log in and on-premises network detection
- Deep visibility into users and applications including user login portal and workspace
- Continuous application health monitoring to ensure that ports are available and users can connect to the application
- Scalable, high-availability edge platform that includes application delivery controller, load balancers, failover, and high availability
- Integrated real-time monitoring and reporting about applications and users
- Programmatically provision using API or SDK with existing enterprise solutions for ease of use reporting functionality
- Flexible SIEM log integration, including an application with Splunk and 365-day
log retention for better reporting